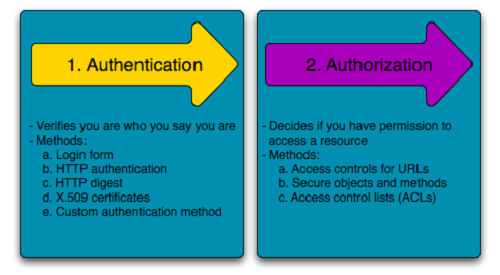
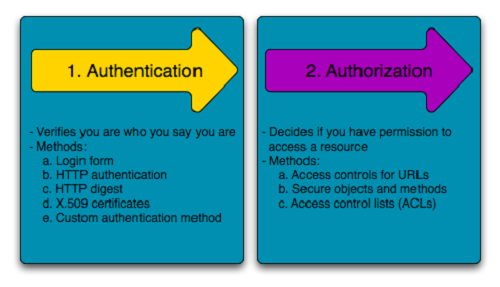
Today I?m going to discuss two topics that most people tend to confuse. Both the terms are often used in conjunction with each other when it comes to security and gaining access to the system. Both terms very key topics that are often associated with the web as key pieces of its service infrastructure. However, both these terms are quite different with completely different concepts. Now you?re wondering what these terms are, well they are known as authentication and authorization. Authentication means confirming your own identity, whereas authorization means being allowed access to the system. In even more simpler terms authentication is the process of verifying oneself, while authorization is the process of verifying what you have access to.
Authentication
Authentication is about validating your credentials such as Username/User ID and password to verify your identity. The system then checks whether you are what you say you are using your credentials. Whether in public or private networks, the system authenticates the user identity through login passwords. Usually authentication is done by a username and password, although there are other various ways to be authenticated.
Authentication factors determine the many different elements the system uses to verify one?s identity before granting the individual access to anything. An individual?s identity can be determined by what the person knows, and when it comes to security at least two or all the three authentication factors must be verified in order to grant someone permission to the system. Based on the security level, authentication factors can vary from one of the following:
- Single- Factor Authentication: This is the simplest form of authentication method which requires a password to grant user access to a particular system such as a website or a network. The person can request access to the system using only one of the credentials to verify one?s identity. For example, only requiring a password against a username would be a way to verify a login credential using single- factor authentication.
- Two- Factor Authentication: This authentication requires a two- step verification process which not only requires a username and password, but also a piece of information only the user knows. Using a username and password along with a confidential information makes it that much harder for hackers to steal valuable and personal data.
- Multi- Factor Authentication: This is the most advanced method of authentication which requires two or more levels of security from independent categories of authentication to grant user access to the system. This form of authentication utilizes factors that are independent of each other in order to eliminate any data exposure. It is common for financial organizations, banks, and law enforcement agencies to use multiple- factor authentication.
Authorization
Authorization occurs after your identity is successfully authenticated by the system, which therefore gives you full access to resources such as information, files, databases, funds, etc. However authorization verifies your rights to grant you access to resources only after determining your ability to access the system and up to what extent. In other words, authorization is the process to determine whether the authenticated user has access to the particular resources. A good example of this is, once verifying and confirming employee ID and passwords through authentication, the next step would be determining which employee has access to which floor and that is done through authorization.
Access to a system is protected by authentication and authorization, and they are frequently used in conjunction with each other. Although both have different concepts behind then, they are critical to the web service infrastructure, especially when it comes to being granted access to a system. Understanding each term is very important and a key aspect of security.
Difference between Authentication and Authorization
Both the terms are often used in conjunction with each other in terms of security, especially when it comes to gaining?
www.differencebetween.net
- OAuth 2 In Action by Justin Richer and Antonio Sanso