There are numerous ways that are used by hackers all the time. Some ways are simple while some are difficult. But since lots of ways are unknown to the people except hackers, these methods are used frequently. One such method is to hack a phone using SMS. Cybersecurity researchers have revealed a critical and undetected vulnerability in SIM cards that could allow hackers to access a smartphone just by sending an SMS.
You can also download our app from playstore:-
https://play.google.com/store/apps/details?id=com.techbull.olympia
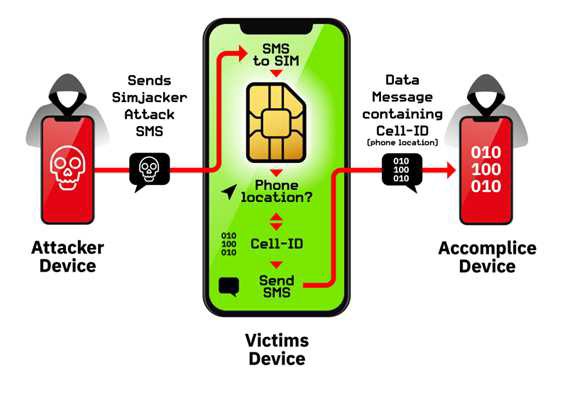
Renowned as ?SIMJacker,? the vulnerability lies at a specific area of the software, named ?S@T Browser.? This browser is attached to most of the SIM cards that are used by mobile operators in at least 31 countries. Regardless of the type of phone that the victim is using, anyone can hack the smartphone through an SMS.
S@T Browser stands for the SIMalliance Toolbox Browser, which is an application installed on almost every SM card as a part of the SIM Tool Kit. Generally, it offers the users basic services, value services, and subscriptions to the customers. The browser contains a series of instructions like setup call provide local data, run a command, send a short message, launch browser, and send data. The software can be exploited to send an SMS, which can also run harmful commands on the phone.
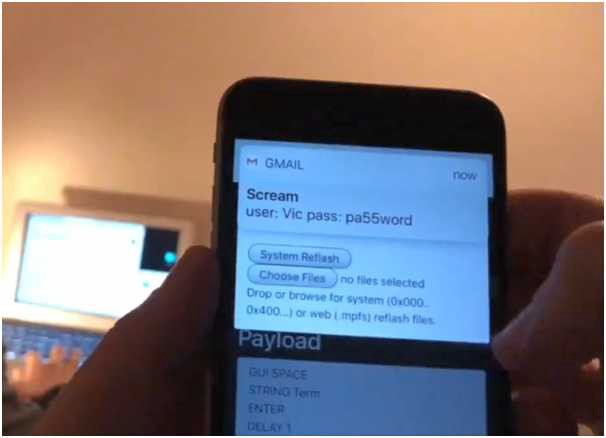
According to the recent research report by AdaptiveMobile Security, a $10 GSM modem is used to exploit the vulnerability in the SIM card.
 Source: AdaptiveMobile Security
Source: AdaptiveMobile Security
?We believe this vulnerability has been exploited for at least the last 2 years by a highly sophisticated threat actor in multiple countries, primarily for surveillance,? security researchers from AdaptiveMobile Security said in a report.
This is how it works:
Step 1: Attackers send a malicious SMS, which is specifically crafted, consisting of binary code (spyware-like code) like spyware on the phone they want to hack.
Step 2: On receiving the SMS, the device is hacked as soon as the person clicks on the malicious link given in the SMS.

Step 3: Hackers get complete access to the phone and can perform any action through remote access.
Step 4: Hackers access the monitored phone?s location and other basic things like screen lock, battery, language, theme, and others.
The target person whose mobile is hacked is unaware of the fact that all the information has been retrieved. SIMJacker attacks took advantage of both complex interfaces and obscure technologies, to show that established defenses are not reliable. It?s worth noting that while some of the commands, such as obtaining a device?s location, don?t require any user interaction, and there is no visual evidence of the attack, others, such as making a call, do require some user interaction on mobile phones.
The hacker could exploit the flaw to:
- Retrieve hacked device? location and IMEI information
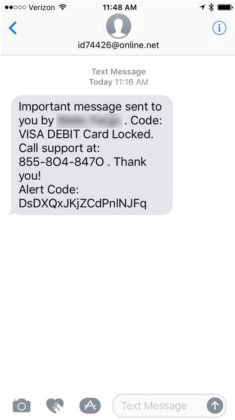
- Spread wrong information by sending fake messages on behalf of the target person
- Perform premium-rate scams by dialing premium-rate numbers
- Spy on victims? surroundings by instructing the device to call the attacker?s phone number
- Spread malware by forcing the phone browser to open a malicious web page
- Perform denial of service attacks by disabling the SIM card
- Retrieve other information like language, radio type, battery level, etc.
The only good news is that the attack doesn?t rely on regular SMS messages, but more complex binary code delivered as an SMS, which means network operators should be able to configure their equipment to block such data traversing their networks and reaching client devices.
However, receiving a wary SMS can make the target person suspicious of the malware. So if you want to hack someone?s phone in a stealth mode, you need another solution.
Alternate Method
Mobile spy apps have become prevalent nowadays. With easy access to the internet and the advancement in technology, now you can hack someone?s phone without even touching their phone. Plus, you don?t even have to make a spy call or send a suspicious SMS to the target device. Mobile monitoring apps work in the background without letting the target person know.
One such mobile hacking app is Xnspy, which gives you access to almost everything stored on the target device. Once subscribed, you can install the app on the target device remotely. The app works in the background and doesn?t consume much battery. The mobile spy app accesses all the information about the online and offline activities of the monitored person and uploads it to its user?s account. It can work with all devices running Android and iOS.
Concluding Remarks
With the proliferation of the internet, hacking tools have become more advanced. You can hack a phone by sending an SMS or by installing a tracking app remotely. Whatever the way you choose, you can get access to someone?s phone without letting them know.
For best fitness workouts Download our app: